Beyond the Breach: Enterprise Password Management Strategies for Securing Corporate Credentials
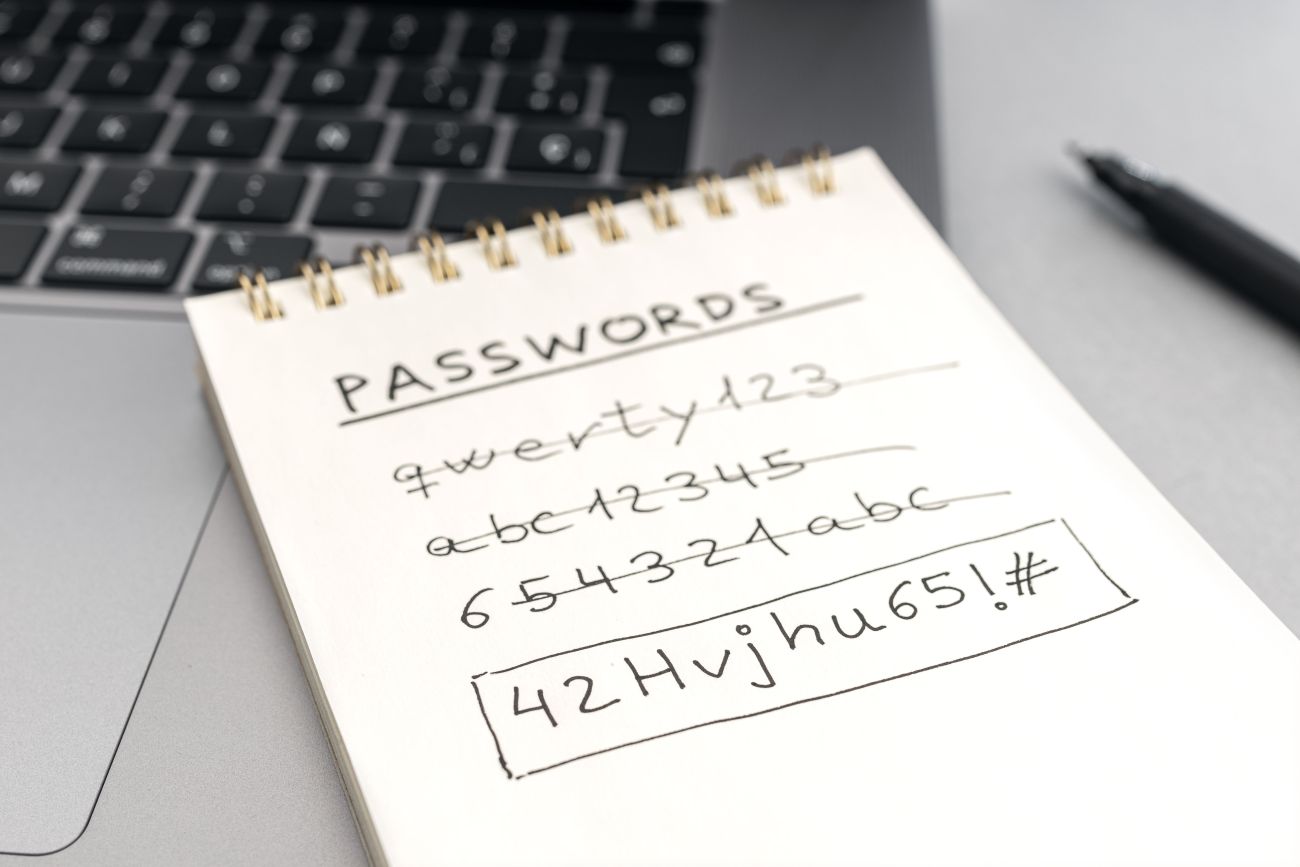
In the modern digital workspace, credentials are the keys to your kingdom. A single compromised password can lead to a catastrophic data breach, regulatory fines, and lasting reputational damage. While individual employees are often the weakest link, the solution lies not just in better training, but in implementing a robust, system-wide Enterprise Password Management (EPM) strategy.
EPM is more than just telling employees to use stronger passwords; it’s a comprehensive security framework designed to govern, protect, and audit every digital credential within an organization. Here are the core strategies for fortifying your corporate perimeter.
1. Centralized Management with a Password Vault 🔑
The foundation of any EPM strategy is the adoption of an enterprise password vault—a secure, encrypted platform designed to store and manage all user and system credentials.
-
The Benefit: A vault eliminates the biggest password risks: reuse, sticky notes, and insecure spreadsheets. Employees only need to remember one strong Master Password to unlock the vault, which then auto-fills complex, unique credentials for all their applications.
-
Actionable Tip: Choose a solution that integrates easily with your existing Single Sign-On (SSO) and identity management systems. Ensure it provides robust auditing capabilities, allowing security teams to track who accessed what credential and when.
2. Enforcing Complexity, Uniqueness, and Rotation ⚙️
Manual password policies often fail because they rely on human diligence. A formal EPM system should automate the enforcement of these critical rules.
-
Complexity: Passwords must be long (16+ characters recommended) and contain a mix of uppercase, lowercase, numbers, and symbols. The vault should generate these randomly to ensure true complexity.
-
Uniqueness: This is non-negotiable. Every account—personal, shared, and privileged—must have a unique password. If one account is breached, it won’t compromise the rest of the network.
-
Rotation: Critical system and shared account passwords (e.g., social media logins, service accounts) should be automatically rotated by the EPM system on a scheduled basis, typically every 60 or 90 days.
3. The Imperative of Multi-Factor Authentication (MFA) 📲
Even the best EPM system is vulnerable if the master password is phished or stolen. Multi-Factor Authentication (MFA) is the essential compensating control that adds a second layer of defense.
-
What it is: MFA requires the user to provide two or more verification factors to gain access, such as: something they know (password), something they have (phone/token), or something they are (biometric data).
-
Deployment Strategy: Enforce MFA on every critical corporate account, especially:
-
The Enterprise Password Vault itself.
-
Email accounts.
-
Cloud infrastructure consoles (AWS, Azure, GCP).
-
Remote access and VPN connections.
-
4. Governing Privileged Access Management (PAM) 👑
Privileged accounts (e.g., Domain Admins, root, or accounts with access to sensitive databases) are the prime targets for hackers. Privileged Access Management (PAM) is a specialized subset of EPM that manages these highest-level credentials.
-
Key PAM Features:
-
Just-in-Time Access: Grant privileged access only when needed and automatically revoke it after the task is complete. This minimizes the exposure window.
-
Session Recording: Record all privileged sessions (keystrokes, screen activity) for auditing and forensic analysis.
-
Automatic Credential Injection: The PAM system should inject the privileged password directly into the target system without ever exposing the password to the user.
-
5. Continuous Employee Training and Awareness 🧠
Technology can only mitigate technical risk; human error remains the biggest variable. A persistent and adaptive security awareness program is vital for EPM success.
-
Training Focus: Go beyond basic password rules. Train employees on:
-
Phishing/Smishing Recognition: How to spot social engineering attacks designed to steal the master password.
-
Incident Response: Knowing the immediate steps to take if they suspect a password has been compromised.
-
Vault Best Practices: Ensuring 100% adoption and proper use of the password management tool, including how to securely share credentials only when necessary.
-
Implementing a comprehensive EPM strategy moves your organization from reactive security (dealing with breaches) to proactive security (preventing them). By centralizing control, automating security policies, and layering on MFA, you can secure those critical corporate credentials and significantly reduce your overall cyber risk profile.
