
Artificial Intelligence (AI) has revolutionized productivity, but like any powerful technology, it is a double-edged
READ MORE
Your password is a lock on a door. But what if a criminal has a
READ MORE
Our mobile phones and tablets are no longer just communication tools; they are our wallets,
READ MORE
Email spoofing is one of the most effective tactics cybercriminals use today. It’s the process
READ MORE
That free Wi-Fi at your favorite coffee shop, airport, or hotel lobby feels like a
READ MORE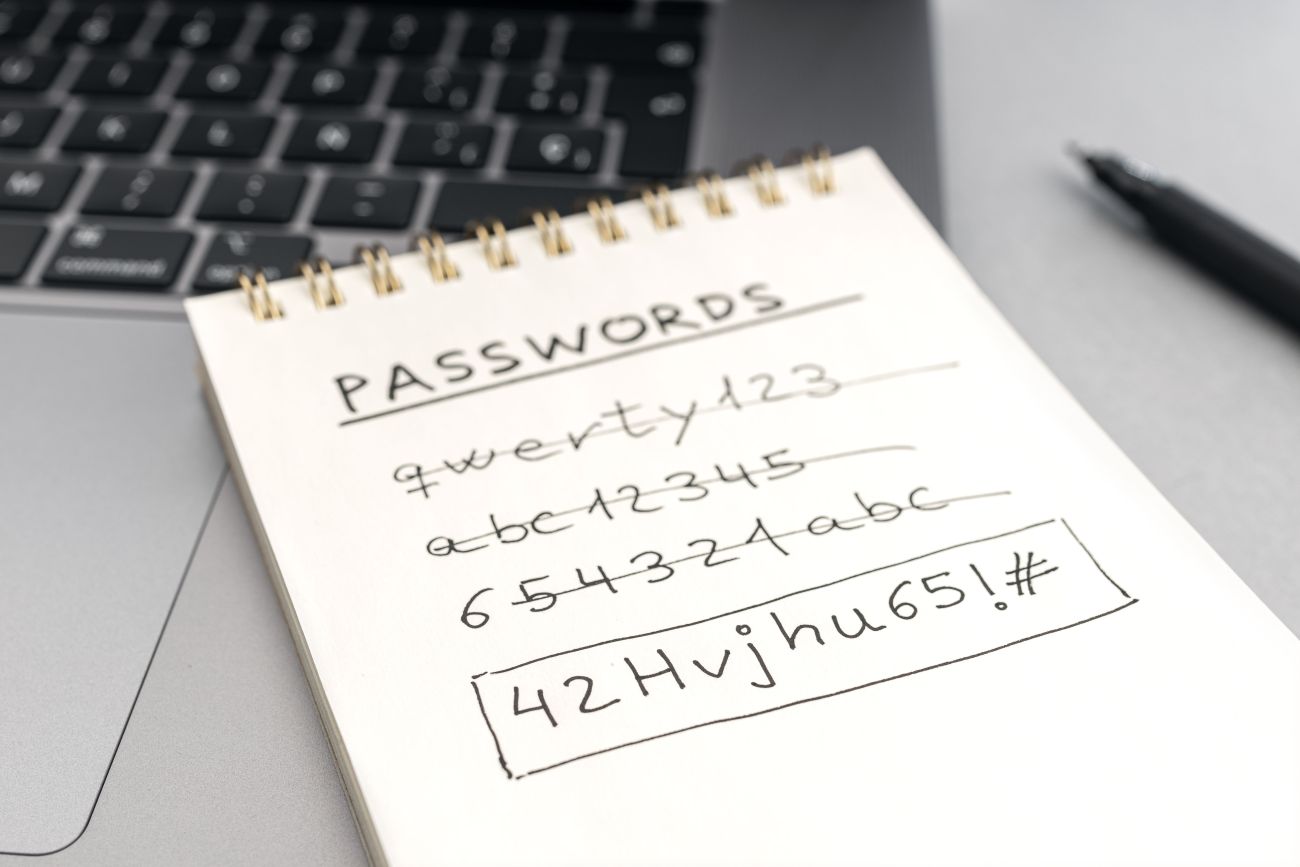
In the modern digital workspace, credentials are the keys to your kingdom. A single compromised
READ MORE